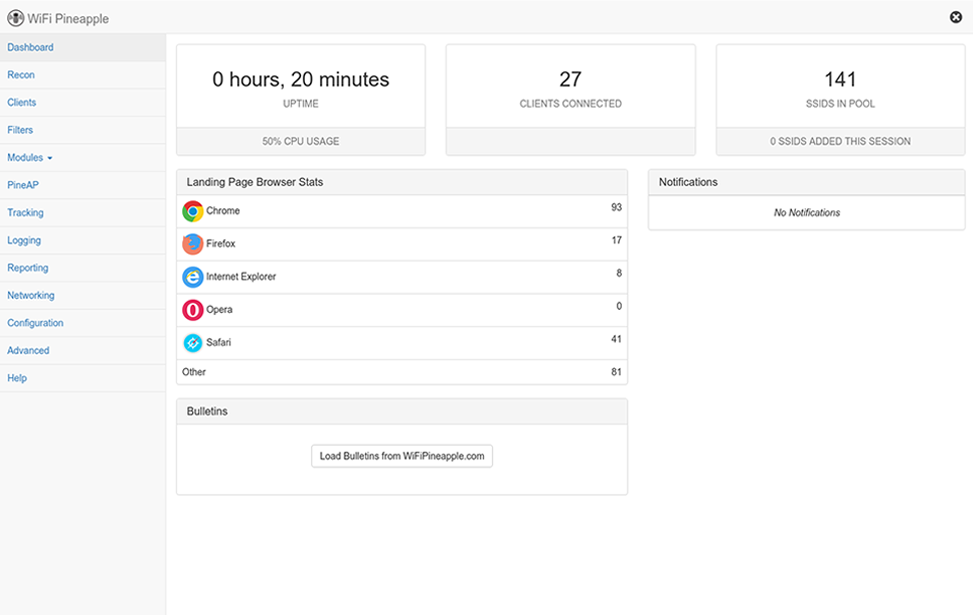
The WiFi Pineapple Interface
With an emphasis on workflow and usability, the WiFi Pineapple NANO introduces a completely re-engineered web interface. Built on modern standards, the new WiFi Pineapple web interface is intuitive, fast, responsive and familiar.
Table views provide a detailed overview of the WiFi landscape. Context menus provide instant access to core PineAP features and modules.
Modules remain a core feature with over the air downloads of community developed add-ons and web front-ends to popular tools. The new API is extremely simple for seasoned developers and newcomers alike.
The PineAP Suite
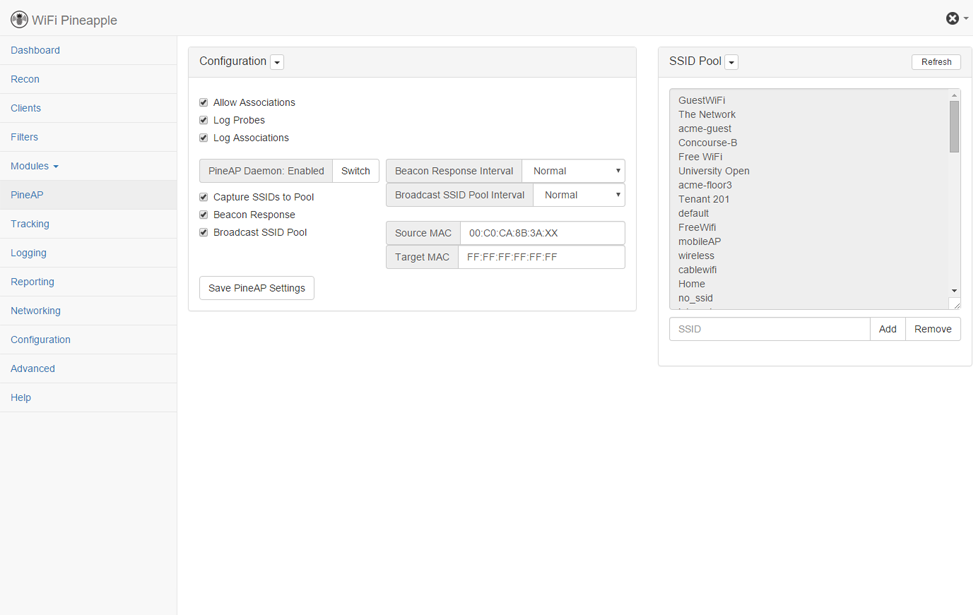
PineAP is a highly effective rogue access point suite for the WiFi Pineapple. Building on the simple probe request and response nature of Karma, PineAP takes the attack to the extreme. By utilizing its purpose engineered software in conjunction with the unique multi-radio design of the WiFi Pineapple, we're able to thoroughly mimic preferred networks with precision client targeting. This sophisticated attack can be launched against key individuals or entire organizations, enabling the penetration tester to precisely orchestrate the airwaves. The end result is a man-in-the-middle position, enabling complete network traffic monitoring and control.
From Bring-Your-Own-Device policy management, to remote access penetration testing - the WiFi Pineapple with PineAP is your wireless auditing solution.
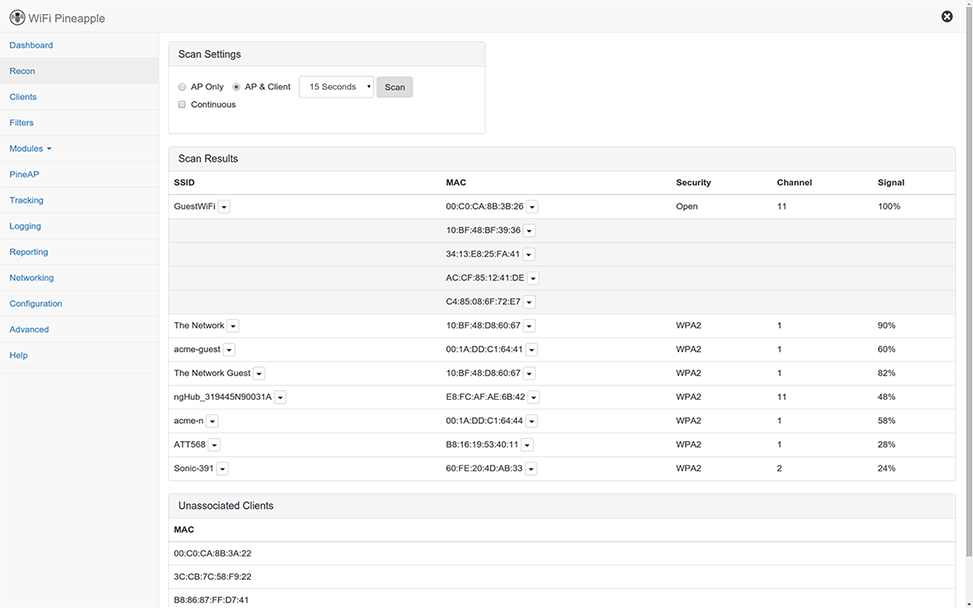
Any successful wireless audit begins with good situational awareness. To that end, the PineAP Recon feature provides the penetration tester with a contextual view of the WiFi landscape. Unlike traditional "war driving", whereby the auditor passively listens for beacons being advertised by Access Points to paint a picture of the surrounding WiFi landscape, the WiFi Pineapple’s Recon Mode goes one giant step further.
By monitoring WiFi channels for all data activity, PineAP's Recon paints a complete picture by showing both Access Points and their respective clients in a parent-child table view. What's more, the elements of the WiFi landscape, such as SSID and Hardware address, support contextual hooks to PineAP functions and WiFi Pineapple modules. By tapping a client or access point, the penetration tester has full control of the situation. If PineAP is the ammunition, Recon is the battlefield.
Respecting the scope of engagement is critical to a successful wireless audit. Limiting the penetration test to specified clients ensures zero collateral damage. PineAP on the WiFi Pineapple supports advanced filtering and targeting capabilities. With allow and deny lists for both SSID and client Hardware address, the PineAP suite prevents unwanted devices from accessing the honeypot network.
Filter by single client of interest or entire organizations - all from the Recon view. In addition to filtering, PineAP is especially effective at snaring individual clients. The entire PineAP attack can be targeted towards a specific device, concealing the attack to bystanders.
Central to the PineAP suite is the self named engine. It combines multiple components to deliver customized attacks. This flexibility gives the penetration tester can gather a wide range of intelligence gathering options. From stealth monitoring to passively honeypots to active and targeted attacks, the PineAP engine is as versatile as it is powerful.
Keeping tabs on the WiFi landscape is made simple with a reporting component, enabling the penetration tester to locally capture, or receive by email, automated reports at set intervals. This is especially useful for unmanned, remotely deployed WiFi Pineapple nodes. Additionally the comprehensive logging engine enables advanced analytics.
Keeping tabs on client devices of interest is also within the realms of PineAP through Tracking. The advanced engine powering the PineAP Recon module enables the penetration tester to execute customized functions whenever devices of interest are seen in the vicinity.
Finally, complementing the PineAP suite is a multitude of community developed modules. Available as free over the air downloads, these modules provide enhancements and additional features to the WiFi Pineapple.
In conclusion, using PineAP on the WiFi Pineapple, the penetration tester is able to immediately identify, audit and analyze vulnerabilities within the wireless landscape.